Domain will continue to point to original owner’s website.
The judge overseeing a lawsuit for Calculator.com has ruled (pdf) that she won’t set aside a Temporary Restraining Order (TRO) that effectively transferred the domain back to the original owner.
Judge Beth Bloom denied Stands4’s request to set aside the TRO. She approved the TRO last week after the original owner of Calculator.com filed a lawsuit saying the domain was stolen.
Here’s the story:
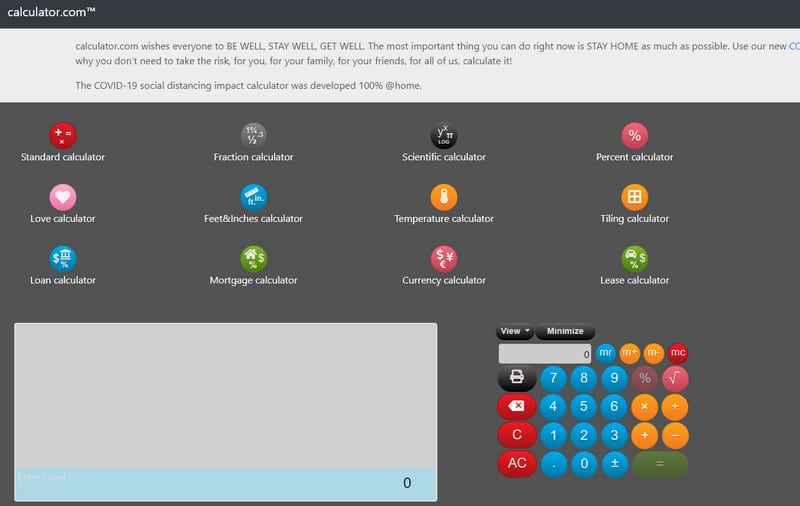
Stands4 says it bought the Calculator.com domain name last month for $180,000 and then spent $50,000 launching a website on it. But the lawsuit alleges the domain name was stolen and that Stands4 might have bought a “hot” domain name.
A purported thief tried to sell the domain on Sedo in 2018, but the buyer canceled the sale after trying to verify ownership.
According to the lawsuit, the thief impersonated the domain owner in 2018 and used false documents to trick Network Solutions into transferring the domain name to him or her. Network Solutions apparently moved the domain back into the correct account but did not revert the contact information to the original owner, so the alleged thief was able to transfer the domain to GoDaddy this year.
The effect of the judge’s decision means that the domain name will point to the Plaintiff’s website not Stand4’s website, for now.




“A purported thief tried to sell the domain on Sedo in 2018, but the buyer canceled the sale after trying to verify ownership.”
Did Sedo or the potential buyer let the domain community know back in 2018 that this name was stolen or at the least potentially stolen?
“Network Solutions apparently moved the domain back into the correct account but did not revert the contact information to the original owner, so the alleged thief was able to transfer the domain to GoDaddy this year.”
i find this interesting. did the original owner not realize the whois was not in their name for almost 2 years?
That stuck out to me too but what is worse yet is NO ONE apparently bothered to be kind enough to mention it to them when it was returned. Not Sedo, not NS not the buyer who backed out when they could not verify. Mind you they need to take personal responsibility for not paying attention themselves as this again could have been avoided so many times its as sad as it is laughable.
That’s what she says. Apparently the thief used an email address similar to her name, which might have tricked her.
The old very similar email replacement trick.
Ill share one element most thieves do not consider most times I say most because rarely one is smart enough to consider it…. IP address.
I kid you not, GD, Web.com have at my request dozens of times now looked closer at IP logs to confirm thefts.
You see, Mr. and Mrs. Smith who have lived in Ohio and only ever accessed their GD account from Ohio do not log in from Iran and discover their name is stolen.
And if you don’t think these RARS’s have the ability to know what the account activity looks like, wake up. They know but unfortunately for the victims the legalities the rar’s could face have them having to stop shirt, understandably in returning names. I am rambling now… But one thing I would demand to know is what IP address logged into the account that held Calculator.com before the theft in 2018, during the time of it and again in 2019-2020.
I would bet a good sum (if I were a betting man) that the IP history to that account tells a very good story!
PS, not only can IP help prove theft but it also can disprove a trade or a thieves attempt at a fake sale to create separation…been there seen that busted by IP! Silly thieves. Very rarely do they cover ALL tracks.
Maybe its how NS decided to return the name in 2018?
Some services alert you to sign-ins from unusual locations. I like how Gmail shows you recent sign in information.
This is true Andrew but it is as simple as the thieves having access to your email for the work around or “delete” of said notification. I suppose with everyone carrying phones now and getting email in their pocket its harder as phone stores text as well but still, work around. I worked a few cases where the thief not only simply kept the victims in a lull by secretly access their email and removing notifications (older couple no email to cell) but even left their site up initially..for YEARS! Some thieves are patient, most not.
If I could spell better I’d write a book lol
If the thief used a good VPN then tracing via IP address is impossible. Someone this sophicated has taken that into account, no doubt. What really irks me is that no one seems capable of tracing where the money went. Are the banks really that clueless ? I see this happening over and over again, ridiculous!
Eva, think more like proving name was accessed from somewhere other than it should be. So VPN or no VPN unless the thief was sure to match exact IP address to the victim, the jig is up! It works in the victims favor when stating their case. Also catching a domain thief via VPN is unrealistic. Building a case for a ring of thieves perhaps, did this with a Russian group some year back with in cooperation with a couple other long time domain members and forum owner. Those Russians were very busy, organized and good at what they did but ultimately left trails.
One thing that a compulsive domain thief usually trips up on is their first theft. If they knew in advance they would steal again they would have been more careful with the first one, from start to finish.
Dan.com and their customer are full of it here:
“Dan.com also advised Stands4 that it undertook significant due diligence to confirm that the domain name seller identified as Chloe Alston was indeed the lawful owner of the calculator.com domain name including, without limitation, review of Chloe Alston’s U.S. issued passport, review of a utility bill provided by Chloe Alston, and review of current and historical WHOIS records for the domain name to confirm that all data corresponded to the data provided by the seller. ”
First off, absent any way to verify a US passport number, the fact that someone can come up with a fake passport is completely unremarkable. Did the facial picture match a Facetime, Skype or Zoom call? Did they bother to conduct one? Why not? Because “Oh, we got a .jpg of a passport here, so it must be real.”
The “current and historical WHOIS records” however, show that the name had been under privacy for years except momentarily near the time of the alleged sale. The problem is that it shows a US address which was the same US address that was shown in the WHOIS data back in 2009.
If you simply Google that address, it is immediately obvious that the house in question was SOLD in 2016, and again in 2018. In fact, you can search the town property records in question online and confirm that the address in the historical WHOIS is most certainly NOT owned by Ms. Alston and her family.
So, if the seller produced a utility bill with that Connecticut address on it (which is the only one in WHOIS) and if Dan.com or the idiot defendant had bothered to check who owns that property from public records, then they would have seen a problem immediately.
But, instead, they stoop pretty far down here to accuse a victim of engaging in fraud based on what is – by their own admission – an obvious failure to conduct competent due diligence.
The moron at Dan.com who was “100% sure” should be taken out and shot.
But, as long as people are going to trust a party to do “due diligence”, when that same party’s commission hangs in the balance, then this is what they get.
Very well said and researched John and I think your final point makes it clear as to why the proper due diligence was not done, if it isn’t incompetence it is greed. And may I add, greed which does not think forward for one second. Imagine brokering a 6 figure trade that you know you did not perform the check on well and not caring, as if there would be no consequence! I can name dozens of stolen domains victims never tried to recover simply because it was not worth the fight, from $XXX-$XXXX values but 6 figures.
The best lessons in life are the one’s we learn from, hoping people take notice of this case and the details that got these parties to this point.
I do not have access to any court filings Andrew/John but do they make it clear whom DAN.com paid out exactly and how?
I can only say that if someone had the balls to steal a name like calculator.com and fake a passport/bills, go to this extent, who here thinks it is their first theft?
Would be time to start looking at that seller more carefully.
“ but do they make it clear whom DAN.com paid out exactly and how?“
Of course not. The silence on that point is loud.